ODINI Malware Defeats Faraday Cages via CPU Magnetic Fields
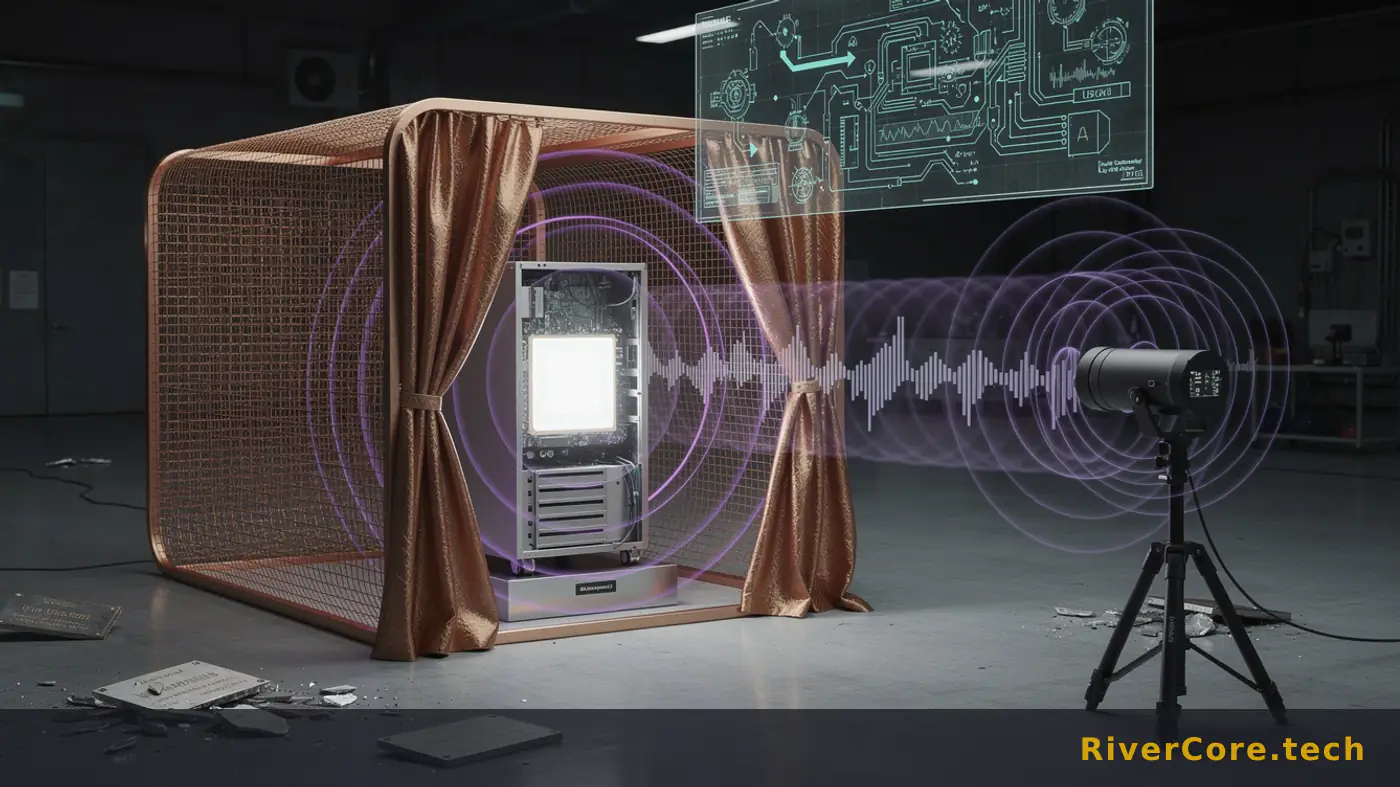
Anyone who has ever signed off on an air-gapped vault build knows the room: copper mesh in the walls, a sign-out sheet for USB drives, and a security architect who promises this is the last line nobody crosses. A proof-of-concept out of Ben-Gurion University just punched a hole in that promise. The attack is called ODINI, and it treats the CPU itself as a radio transmitter.
The implications hit military, financial, and critical infrastructure operators first. Everyone else who runs sensitive workloads behind physical isolation should still be paying attention.
What Happened
On May 11, 2026, researchers led by Mordechai Guri at Ben-Gurion University disclosed ODINI, a proof-of-concept malware that exfiltrates data from air-gapped computers sitting inside Faraday cages. As CyberSecurityNews reported, the technique modulates CPU workload to generate low-frequency magnetic fields that punch straight through standard chassis metal and Faraday shielding alike.
The attack assumes an initial foothold already exists. The Guri team points to supply-chain attacks or compromised USB drives as the realistic entry vectors. Once the implant is running, it doesn't need elevated privileges. It just schedules CPU-heavy computations in a pattern that encodes data onto magnetic emissions.
A receiver placed within 100 to 150 centimeters of the compromised machine, using a dedicated magnetic sensor, pulls the data off the air at a maximum of 40 bits per second. That sounds slow until you remember that a 256-bit AES key fits in under seven seconds of broadcast time. The malware targets exactly that kind of payload: passwords, authentication tokens, encryption keys.
A sibling attack, MAGNETO, uses the same CPU manipulation trick but turns an infected smartphone's magnetometer into the receiver. It works at distances up to 12.5 centimeters and shifts 5 bits per second. The detail that should make every facility security lead twitch: MAGNETO still works when the phone is in airplane mode or inside a Faraday bag.
Guri confirmed the encoding uses both amplitude-shift keying and frequency-shift keying, classic radio modulation schemes adapted to a magnetic carrier. Conventional antivirus and runtime monitoring don't catch it, because nothing on the host looks unusual beyond CPU load.
Technical Anatomy
The physics here is what makes this dangerous. Low-frequency magnetic fields have extremely low impedance. They don't behave like the RF emissions that copper mesh and Faraday geometry are designed to suppress. They pass through chassis steel and cage walls more or less unaffected. That's not a flaw in any specific shielding product. It's a property of the frequency band.
The transmitter side is just a scheduler. The malware spins up tight computational loops on selected cores, then idles them, in a pattern that maps to bits. Dynamic power draw produces fluctuating current through the CPU package and board traces, and current fluctuations produce magnetic fields. No driver, no kernel module, no admin rights. A user-mode process is sufficient.
Encoding uses ASK and FSK because those are the modulation schemes that survive a noisy magnetic environment with cheap receivers. ASK varies signal amplitude to represent bits. FSK varies frequency. Both can be decoded by a small sensor and a laptop running off-the-shelf DSP code. You don't need a state-actor lab to receive ODINI traffic, you need a magnetometer and patience.
The 40 bits per second figure is the ceiling, not the floor. In production incidents I've seen involving covert channels, real-world throughput drops once you account for error correction, retransmits, and motor noise from HVAC and adjacent hardware. Even at a realistic 10 to 20 bps, a determined operator with overnight access to a receiving sensor can pull credentials and keys before the morning shift arrives.
MAGNETO is the more uncomfortable variant for anyone managing facility access. A magnetometer ships in basically every smartphone built in the last decade. Airplane mode disables radios. It does not disable the compass chip. A phone in a Faraday bag, sitting on a desk near an air-gapped workstation, is still a working receiver. That breaks the mental model most secure facilities operate on.
My take: the air-gap was never a security primitive. It was an assumption about adversary effort. ODINI and MAGNETO just dropped that effort by an order of magnitude.
Who Gets Burned
The named exposure is military, financial, and critical infrastructure operators. That's the headline list, and it's accurate. But the real blast radius is wider.
Any iGaming operator running an HSM or offline key ceremony room is in scope. Cold-storage signing for crypto custodians sits in exactly the kind of shielded room ODINI was built to attack. Card scheme certification environments, PCI key management ceremonies, certificate authority root signing events: all of these depend on the premise that a Faraday-shielded room is a one-way data diode. That premise is now contingent.
Teams I've worked with in payments treat the offline ceremony room as a checkbox item, audited once a year, otherwise ignored. The uncomfortable read: those audits don't cover magnetic side channels, because until last week the threat model didn't include them. Expect that to change in the next audit cycle. PCI SSC and similar bodies tend to move slowly, but research like this lands in framework updates within 12 to 18 months.
Crypto custodians have a faster clock. A 40 bps exfil channel against a signing machine is a direct path to seed phrase or private key extraction. If your custody architecture assumed that a malware-infected signing host couldn't talk to the outside world because of physical isolation, that assumption needs a rewrite this quarter, not next year.
Defense and intelligence operators already model emanation security through TEMPEST and similar programs. The mu-metal shielding option exists for them. For everyone else, the source describes mu-metal as prohibitively expensive and impractical, which matches what commercial security teams will find when they price it.
The vendor reaction to watch: HSM manufacturers and secure workstation OEMs. Expect marketing pivots toward "magnetic emanation hardened" SKUs within a year. Most will be theater. A few will be real.
Playbook for Security Teams
This week, four concrete moves.
First, update the threat model for any room you currently call air-gapped. Add magnetic side channel as a documented vector. If the threat model document doesn't change, nothing else will.
Second, enforce strict physical zoning. The source calls this the most reliable defensive measure, and that lines up with operational reality. Ban personal electronics from the immediate vicinity of air-gapped systems. Not "phones in pockets allowed if on airplane mode." Banned. The MAGNETO result kills the airplane-mode exception.
Third, evaluate active jamming. Hardware-based commercial magnetic field generators that produce counter-noise are a defensive option called out in the disclosure. They're expensive but cheaper than mu-metal shielding by a wide margin. Software-based jamming, which schedules random CPU workloads to corrupt any covert signal, is the budget option. It will degrade performance, which is a fair tradeoff on a signing host that runs ceremonies twice a quarter.
Fourth, tighten the initial infection vectors. ODINI assumes someone got code onto the air-gapped host. That means USB hygiene and supply-chain controls are still your first line. Cross-check your software bill of materials against recent supply chain incidents in the CVE database, and map your detection coverage against the relevant exfiltration techniques in MITRE ATT&CK. If your USB onboarding process still relies on a single-station scan, fix that before worrying about magnetic fields.
One sharp line for the security architects reading this: if your isolation strategy depends on a property of the universe you can't name, you don't have an isolation strategy.
Key Takeaways
- ODINI exfiltrates data from Faraday-caged air-gapped computers at up to 40 bits per second using CPU-generated magnetic fields, with no admin privileges required.
- MAGNETO variant uses a smartphone magnetometer as receiver at 12.5 cm range, and works even when the phone is in airplane mode or inside a Faraday bag.
- Conventional Faraday cages don't block low-frequency magnetic transmissions, and mu-metal shielding is too expensive for most commercial deployments.
- Crypto custody, PCI key ceremonies, and certificate authority signing rooms are all in scope, not just military and government facilities.
- Strict physical zoning that bans external electronics near air-gapped systems remains the most reliable defense, with active magnetic jamming as a secondary control.
Frequently Asked Questions
Q: How does ODINI bypass a Faraday cage when that's exactly what Faraday cages are designed to prevent?
Faraday cages are designed to block higher-frequency electromagnetic radiation, the kind used in radio and Wi-Fi. ODINI operates in the low-frequency magnetic band, where signals have extremely low impedance and pass through standard chassis metal and Faraday shielding largely unaffected. Blocking it requires ferromagnetic materials like mu-metal, which the researchers describe as prohibitively expensive.
Q: Is ODINI being used in real attacks today?
ODINI is a proof-of-concept disclosed by academic researchers at Ben-Gurion University, not a malware family observed in the wild as of the disclosure. That said, proof-of-concept covert channel work from this team has historically informed real-world tradecraft, and the technique requires no exotic hardware on the receiver side. Treat it as a credible near-term threat for high-value targets.
Q: What's the single most effective defense if mu-metal shielding isn't an option?
Strict physical zoning policies that ban all external electronic devices from the immediate area around air-gapped computers. The source identifies this as the most reliable defensive measure. Combine it with active hardware-based magnetic jamming for high-value rooms, and tighten USB and supply-chain controls to prevent the initial infection that ODINI depends on.
ShinyHunters Hits Canvas: 9,000 Universities, 275M Records Claimed
ShinyHunters claims 275 million records from 9,000 universities via a single Canvas teacher account. The blast radius math is the story, not the ransom note.
The Identity Bill Comes Due: Cisco, ServiceNow Bet on Non-Human Auth
Cisco buys Astrix, ServiceNow ships Autonomous Security & Risk, XBOW closes $155M. The non-human identity bill is landing on CFO desks this quarter.
Dirty Frag Zero-Day Hands Root on Every Major Linux Distro
A nine-year-old bug in the Linux kernel's crypto interface just became a one-command root exploit. No patches, no CVE at first, and the embargo is already in pieces.